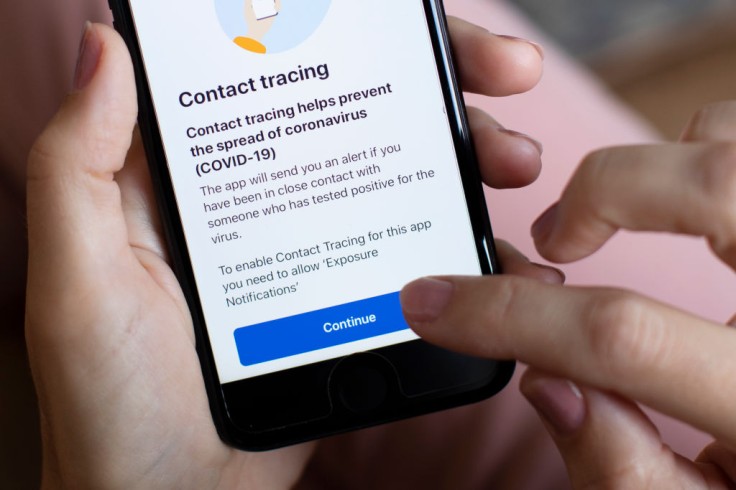
With the sudden outbreak of the pandemic, technological programs took a leap of action to help alleviate the crisis. One of these programs is Apple and Google's COVID-19 contract tracing tool that quickly became essential on tagging people's locations, activities and interactions. However, new research showed that these contact tracing pass might be stealing more information than you know.
IOS and Android have dominated the mobile systems and have been at odds with competing in their performance over these last few years. Gizmodo, however, reported that these two partnered up to create an efficient and widespread COVID-19 contact tracing technology last year. This feature was promised to uphold privacy conditions, where all data collected would remain relatively anonymous and only public health agencies can access it.
Unfortunately, the Android version was discovered to have significant flaws.
Android COVID-19 Contact Tracing Tool Can Leak Sensitive Information
The contact-tracing tool uses anonymized Bluetooth signals to recognize other phones, which has the feature enabled. These signals change every 15 minutes to ensure that uses are not identifiable. These signals are then saved to the Android device's system logs.
Android is marketed for its open-source nature, creating a platform that flourishes under both corporate and indie developers. However, some researchers report that Android has a significant privacy flaw that allows the other pre-installed apps to access sensitive data.
A mobile security firm called AppCensus tested the Android and iPhone contact tracing system and discovered that logs show sensitive data like an encounter with a person tagged to be positive for COVID-19. The data also showed the device name, MAC address, and advertising ID--the data Google Play services use to personalize ads. AppCensus claimed to report the issue to Google and has been repeatedly dismissed on the topic.
Google Response and Fix
According to Gizmodo, a Google spokesperson responded with an argument that no one has direct access to these logs.
"With the Exposure Notification system, neither Google, Apple, nor other users can see your identity, and all of the Exposure Notification matchings happens on your device... These Bluetooth identifiers do not reveal a user's location or provide any other identifying information, and we have no indication that they were used in any way - nor that any app was even aware of this," the spokesperson shared.
Google also replied that the Bluetooth identifiers are temporarily accessible to some preinstalled applications only for debugging purposes. Unfortunately, there are no official means to check how much information an Android device might have leaked. However, it is important to note that this flaw was not found in the iOS contact-tracing framework.
The tech giant also noted that it has started to implement an update for the debugging issue and should be completed soon, meaning the temporary access could be gone soon.
During the feature's rollout, Google announced that all necessary contact tracing data would be stored locally to the device and not sent to any cloud storage for processing. Nonetheless, tests from other researchers argue that the opposite is true. To avoid leaking any more data, turn off the contact-tracing feature from your Android device when not in use.
Related Article: Digital Vaccine Passport: Benefits, Issues, and How to Set Up Your Excelsior Pass Online









